How Developers Can Extract OTPs Without Brittle Regex
Kieran Goodary
Why is extracting OTPs from emails a common pain point for developers?
If you've ever written end-to-end tests or integrated authentication flows, you've probably faced the quirky world of one-time passwords (OTPs) sent via email. On the surface, grabbing an OTP from an email might seem trivial. But as anyone who's tried to write a regular expression that works on all OTP emails quickly learns, it’s anything but.
The problem often boils down to fragile parsing logic. Emails arrive in all sorts of formats — HTML, plain text, embedded images — and OTPs themselves come in countless styles: four digits, six digits, alphanumeric, with spaces, dashes, or hidden in weird sentence structures. To top it off, different apps or services might change their email templates slightly over time, which breaks your carefully crafted extraction logic.
This brittleness not only makes your test suite flaky but also wastes engineering time on chasing down false negatives. So, how can you untangle this mess?
Why is relying on regex for OTP extraction inherently brittle?
Regular expressions are powerful but blunt instruments. They excel when you have predictable, well-structured input, but email OTPs rarely fit that bill.
A typical regex to extract a 6-digit numeric code might look like /\b\d{6}\b/. Simple enough. But such patterns quickly run into trouble when:
- OTPs are spaced out (e.g., "1 2 3 4 5 6") or separated by dashes
- Emails include multiple numbers (dates, order numbers, phone numbers)
- The OTP includes letters (alphanumeric tokens)
- Formatting changes without notice
Moreover, regex-based extraction often ignores the context around the OTP. For example, an email might say "Use 123456 as your OTP", making it easy to isolate "123456". But if the email says "Your order number is 123456 and your OTP is 654321", a naive regex might grab the wrong number.
In CI pipelines or automated testing, these little mismatches translate into flaky tests and wasted debugging cycles — the enemy of developer sanity.
How can developers design more reliable OTP extraction methods?
There are a few approaches that reduce reliance on brittle regexes and deliver more reliable OTP extraction:
1. Use specialized email testing inbox APIs
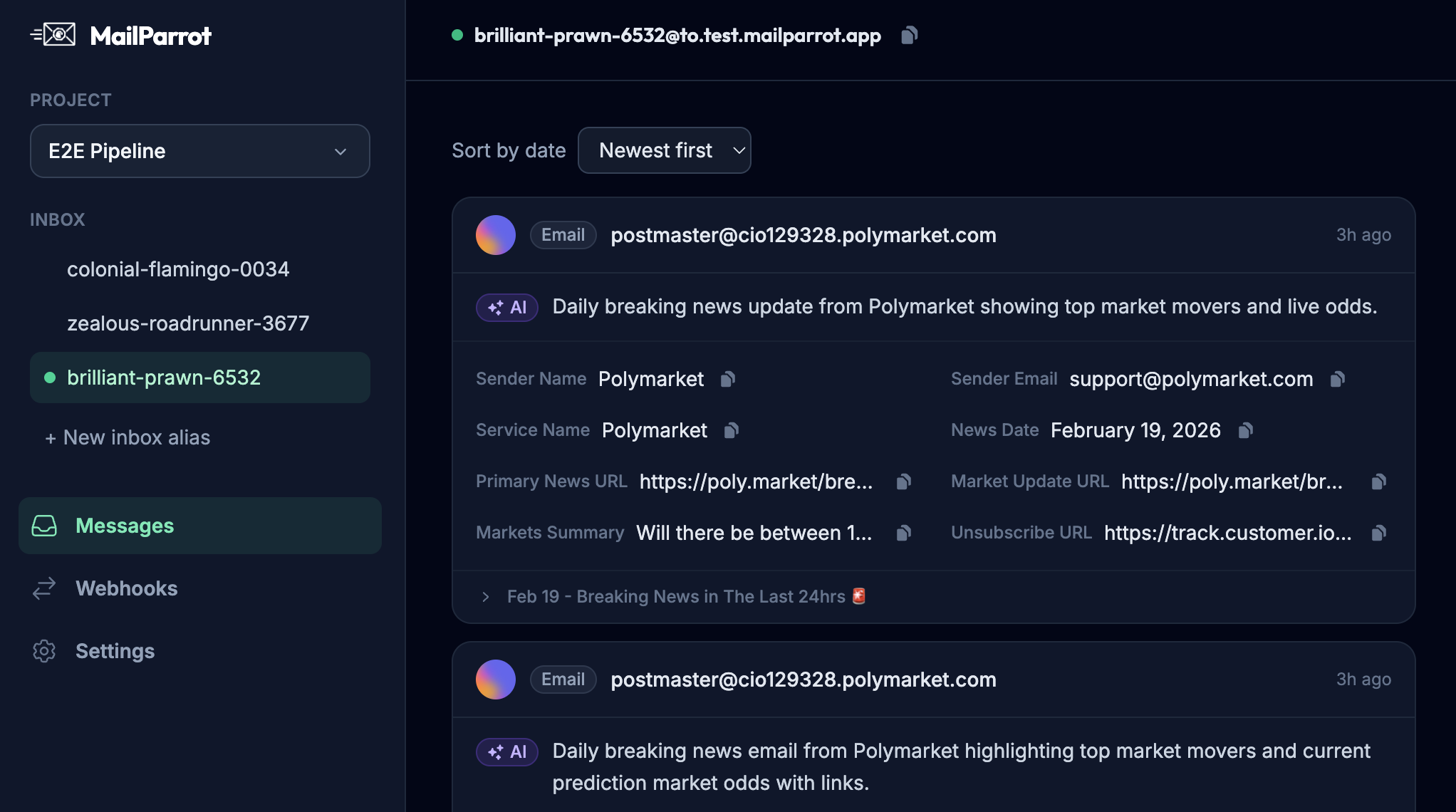
Instead of shuffling through unpredictable inboxes or shared mailboxes, use disposable inboxes with APIs designed for automated email parsing. Services like MailParrot (yep, shameless plug, but we use it for exactly this) provide structured access to the latest email data, including parsing common patterns and allowing you to match emails by subject or sender.
With such APIs, you can fetch the email payload directly and use the metadata to narrow down the right message before parsing the OTP.
2. Parse emails with semantic hints, not just pure regex
Instead of purely pattern matching on numbers, look for contextual anchors: phrases like "Your OTP is", "Use the code", "verification code", etc. By extracting the sentence or paragraph containing these phrases, you reduce false positives significantly.
Combine this with targeted regex within the narrowed context. So instead of scanning the whole email for six digits, extract the sentence with "OTP" in it, then run the digit match.
3. Take advantage of structured or machine-readable formats
Some providers embed OTPs in JSON payloads within the email via scripts or in email headers for developers. This is less common but worth checking if you're controlling both sending and receiving ends.
4. Leverage natural language processing (NLP)
If your use case is complex, lightweight NLP models or even simple heuristic rules can identify OTPs with better accuracy. For example, annotating key terms and classifying token candidates rather than grepping blindly.
That might sound like overkill, but modern tools and APIs make lightweight NLP accessible.
How can MailParrot help in extracting OTPs without brittle regex?
MailParrot offers an inbox API that’s purpose-built for developers who need reliable email data in test and automation environments. Here’s what makes it better:
-
Disposable inboxes: Spin up throwaway inboxes on demand to catch OTP emails separately without polluting shared mailboxes.
-
Webhook support: Get real-time push notifications on incoming emails, so your tests can react immediately instead of polling.
-
Structured email data: Access parsed email content including subject, headers, and body separately.
-
Built-in OTP extraction: MailParrot’s API includes built-in heuristics for common OTP patterns, reducing the need to write your own regex.
Using such APIs, you avoid managing flaky regexes against messy raw email content. Instead, you get clean, consumable data that fits perfectly into modern CI/CD pipelines.
What are the risks of using shared Gmail accounts and homemade regex
in OTP extraction workflows?
Many teams fall into the trap of using shared Gmail accounts or similar general-purpose inboxes combined with homemade regexes to extract OTPs. Here’s why that’s a recipe for disaster:
-
Email collisions: Multiple tests or developers checking the same inbox lead to race conditions. One test consumes the email and deletes it, causing others to fail.
-
Multiple messages: A shared inbox often has hundreds of emails; filtering becomes unreliable.
-
Changing templates: Relying on regex means any change to email format breaks your extraction.
-
Pollution and security: Shared inboxes are less private and prone to leaks.
In a nutshell, this approach leads to flaky automation, wasted engineering time, and possible security issues.
How does reliable OTP extraction improve automated testing and CI/CD?
Imagine a test scenario for a mobile or web app requiring login via OTP emailed to the user. Automating this flow means reading the OTP from email programmatically.
If the OTP extraction is flaky, the entire test pipeline becomes brittle:
-
False negatives: Tests fail because OTP wasn’t read correctly, not because the code is broken.
-
Delays: Tests retry or wait longer for emails, slowing down CI pipelines.
-
Developer frustration: Hunting down regex bugs instead of improving code.
Replacing brittle regex with robust extraction strategies:
-
Increases test reliability: Tests fail only when there’s a real problem.
-
Speeds up feedback: Immediate OTP extraction via API/webhook keeps pipelines snappy.
-
Simplifies maintenance: Less regex chasing means your automation code stays tidy.
This is crucial when running thousands of tests or when your authentication flows are critical to business.
What practical steps can developers take today to avoid brittle OTP extraction?
Here’s a no-nonsense checklist:
-
Stop using shared Gmail for tests. Use disposable inbox services or set up dedicated test accounts with APIs.
-
Leverage the email metadata. Use email subject, sender, and headers to find the right message before parsing.
-
Extract OTPs contextually. Look for keywords around the OTP instead of blind digit matching.
-
Use or build structured parsers. Consider existing libraries or services that parse email HTML and text.
-
Automate with webhooks. Get email data pushed to your tests instead of polling inboxes.
-
Monitor and update. Email templates change. Build alerts or tests to catch breaking changes early.
Can developers build custom OTP extraction tools or should they rely on third-party services?
If your OTP emails are simple and stable, a lightweight in-house solution might suffice. But as complexity and volume grow, maintaining your own extractor becomes a distraction and risk.
Third-party services specializing in disposable inboxes and OTP extraction:
- Reduce operational overhead
- Provide ready-made, battle-tested APIs
- Offer scalability and reliability
That said, it’s essential to vet providers for security and data privacy.
For many teams, a hybrid approach works best: start simple, and evolve to specialized services as needs grow.
Final thoughts: Make OTP extraction boring and reliable
OTPs are a small but critical cog in the auth machine. Treating their extraction as a quick hack leads to flaky tests and developer headaches.
Instead, invest in reliable, context-aware OTP extraction that can survive changing email formats and diverse flows. Use disposable inbox APIs, semantic analysis, and real-time webhooks to build a robust foundation.
Make your OTP extraction so reliable it’s boring — because boring is exactly what you want in test automation.
Happy coding!
Ready to unblock your tests and pipelines?
1,000 free credits with every account-no card required. They don’t expire.
Get started for free